Handed out: Oct. 3, 2005
Due back: Oct. 16 11:59pm (by submission timestamp).
Submission: Electronic upload submission (see instruction online at the course webpage)
Notes: 1. To be done individually.
2. Please do not give a simple yes/no as results to some of the questions.?Briefly explain why and how you achieve that result.
1.
Please classify each
of the following as a violation of confidentiality, of integrity, of
availability, of authenticity, or of some combination of those.
1.
John copies Mary's
homework.
2.
Paul crashes Linda's
system.
3.
Carol changes the
amount of Angelo's check from $100 to $1000.
4.
Gina forges Roger's
signature on a deed.
5.
Rhonda registers the
domain name "AddisonWesley.com" and refuses to let the publishing
house buy or use that domain name.
2.
Token cards
display a number that change periodically, perhaps every minute. Each such
device has a unique secret key. A
human can prove possession of a particular such device by entering the
displayed number into a computer system.
The computer system knows the secret key of each authorized device. How would you design such a device?
3.
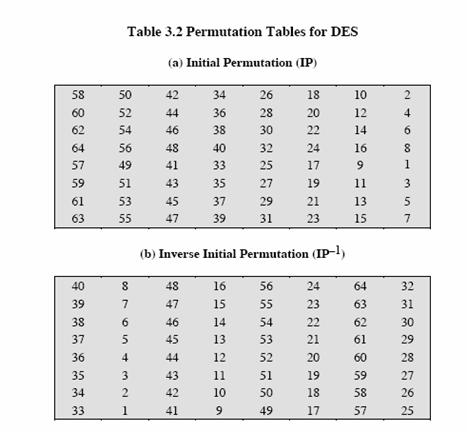
KPS problem 3-5
Supose the DES
mangler function mapped every 32-bit value to zero,
regardless of the value of its input. What function would DES then compute?
4.
KPS problem 6-3
In RSA, is it possible for more than one d to work with a given e, p and q?
5.
Stallings problem 3.7
(b �C d)
This problem provides a numerical example of encryption using a one-round version of DES. We start with the same bit pattern for the key and the plaintext, namely,
In hexadecimal notation: 0 1 2 3 4 5 6 7 8
In binary notation: 0000 0001 0010 0011 0100 0101 0110 0111
1000 1001 1010 1011 1100 1101 1110 1111
We provide the answer to (a) as:
In binary notation: 0000
1011 0000 0010 0110 0111
1001
1011 0100 1001 1010 0101
In hexadecimal notation: 0
B 0 2 6 7 9 B 4
a) Derive K1, the first-round subkey.
b) Derive L0, R0.
c) Expand R0 to get E[R0].
d) Calculate ![]()
6.
Stallings problem 9.2
(a) (c) and (e)
Perform encryption and decryption using the RSA algorithm, as in Figure 9.6 for the following:
a. p = 3; q = 11, e = 7; M = 5
c. p = 7; q = 11, e = 17; M = 8
e. p = 17; q = 31, e = 7; M = 2. Hint: Decryption is not as hard as you think; use some finesse.
7. Stallings problem 9.3
In a public-key system using RSA, you intercept the ciphertext C = 10 sent to a user whose public key is e = 5, n = 35. What is the plaintext M?
8.
Exercises on GNU
Privacy Guard, an open-PGP tool
Introduction of GnuPG
GnuPG is a complete and free replacement for PGP (Pretty Good Privacy, a public
key encryption program developed by Philip
R. Zimmermann). GnuPG
stands for GNU Privacy Guard and is GNU's tool for
secure communication and data storage. It can be used to encrypt data and to
create digital signatures. It includes an advanced key management facility and
is compliant with the proposed OpenPGP Internet
standard as described in RFC 2440.
Environment
Almost every Linux distribution includes the GnuPG package. On T-lab machines, students can use gpg command to use GnuPG. The current version on T-lab is version
1.2. For more information about
T-lab, check out http://www.cs.northwestern.edu/support/resources/tlab.php
Tasks
- Copy the skeleton tarball from /home/yga751/cs395-hw1.tar.gz on any
T-lab machine and uncompress it
- Generate a key-pair
Put your netid in the name field,
and put CS
- Export your public keys save as <netid>.pubkey
Hint: use --armor to make the public key readable
- Get the fingerprint of the public key and save as
<netid>.figprt
Import
cs395.pubkey from the skeleton package
- Encryption
- Edit cs395-encrypt.test to add your netid as the first line
- Encrypt cs395-encrypt.test as
cs395-encrypt.test.asc
Hint: use �Carmor and the recipient should be CS395
- Verify and decrypt the signed file cs395-dsig.test,
save as cs395-dsig.test.orig
- Create detached signature
- Use the file cs395-encrpt.test (with your netid as the first line)
- Create a detached signature as
cs395-encrypt.test.detachsig
Hint:
use --armor to make it readable
- Generate a revoke certificate for your private key,
and save it as <netid>.revoke
Hint use �Carmor to make it readable
Submission
Use handin.sh <netid> to make a tarball of
the project, which contains the following results:
- <netid>.pubkey, <netid>.figprt, <netid>.revoke
- cs395-encrypt.test, cs395-encrypt.test.asc,
cs395-encrypt.test.detachsig
- cs395-dsig.test, cs395-dsig.test.orig
- Write a document file as readme.txt and include a list of
commands that you used for this project, in the order of project tasks.
- Your answers to problems 1-7
should be included in another file, hw1.txt.
Follow the homework submission link on the course webpage
to upload your file.
References:
http://www.gnupg.org/gph/en/manual.html
http://webber.dewinter.com/gnupg_howto/english/GPGMiniHowto.html
http://www.gnupg.org/(en)/documentation/faqs.html